Deploy to MAAS
This guide provides you with the steps to deploy a PCG cluster to a MAAS environment. Before you begin the installation, carefully review the Prerequisites section.
Prerequisites
-
A Palette API key. Refer to the Create API Key page for guidance.
warningThe installation does not work with Single Sign-On (SSO) credentials. You must use an API key from a local tenant admin account in Palette to deploy the PCG. After the PCG is configured and functioning, this local account is no longer used to keep the PCG connected to Palette, so you can deactivate the account if desired.
-
Download and install the Palette CLI from the Downloads page. Refer to the Palette CLI Install guide to learn more.
-
You will need to provide the Palette CLI an encryption passphrase to secure sensitive data. The passphrase must be between 8 to 32 characters long and contain a capital letter, a lowercase letter, a digit, and a special character. Refer to the Palette CLI Encryption section for more information.
The following system requirements must be met to install a PCG in MAAS:
-
PCG IP address requirements:
- For a single-node gateway, one IP address must be available in the MAAS subnet for the PCG, or three available IP addresses for a three-node gateway. Refer to the PCG Sizing section for more information on sizing.
- One IP address must be available in the MAAS subnet for the Kubernetes API-server endpoint when deploying a three-node gateway.
- One IP address reserved for cluster repave operations.
- One IP address for the Virtual IP (VIP).
- DNS can resolve the domain
api.spectrocloud.com.
-
An x86 Linux environment with a Docker daemon installed and a connection to Palette and the MAAS endpoint. The Palette CLI installation must be invoked on an up-to-date Linux system with the x86-64 architecture.
-
Sufficient IP range available within the configured MAAS subnets.
warningBy default, the MAAS Kubernetes pack uses a pod Classless Inter-Domain Routing (CIDR) range of 192.168.0.0/16. Ensure that the pod CIDR range for any clusters you deploy after setting up the PCG does not overlap with the network used by the bare metal machines that MAAS manages.
-
Each node in the PCG cluster requires a machine from MAAS in a ready state with the following resources:
- CPU: 4
- Memory: 8192 MiB
- Storage: 60 GiB
For production environments, we recommend using three nodes, each with 100 GiB of storage, as nodes can exhaust the 60 GiB storage with prolonged use. If you initially set up the gateway with one node, you can resize it later.
-
An active MAAS API key. Refer to the Authenticating to the MAAS API guide to learn more about how to create an API key.
-
The DNS server that the PCG installer will use must be able to resolve the DNS names of machines that MAAS deploys so it can connect to them. The default setup is to use the MAAS server as the DNS server for any bare metal servers that it deploys. The default MAAS DNS zone is
.maas. You can use.maasor the MAAS web console to create a new DNS zone. When you deploy the PCG and clusters, you can select the desired DNS zone in which DNS name records should be created.In the MAAS subnet configuration, you can specify which DNS servers those servers in the MAAS subnet should use.
warningIf you configure a DNS server other than the MAAS DNS server, you must create a DNS delegation so that it can forward DNS requests for zones that are hosted by MAAS to the MAAS DNS server.
The installation process first requests machines from MAAS and then must connect to them. To connect, the installation
process attempts to use the Fully Qualified Domain Name (FQDN) of the server. If you used .maas as the default DNS
zone, the FQDN would be machine-hostname.maas.
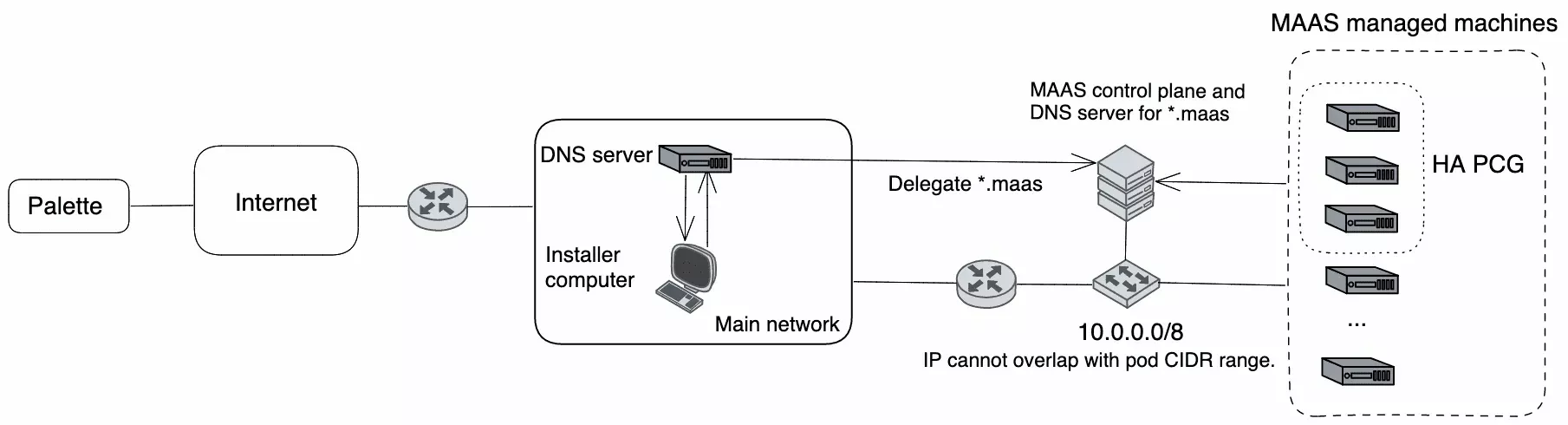
The diagram below shows an example of using an external DNS server for servers that MAAS deploys in addition to a DNS delegation. This ensures all servers in the network can resolve the DNS names of servers deployed by MAAS. Note that it is not required for the DNS records to be accessible from the internet.
Deploy PCG
-
On your Linux host with the Palette CLI installed, open a terminal session.
-
Create a Palette CLI encryption passphrase and set it as an environment variable. Replace
<palette-cli-encryption-passphrase>with your passphrase.export PALETTE_ENCRYPTION_PASSWORD=<palette-cli-encryption-passphrase> -
Issue the following command to authenticate your Palette CLI installation with Palette. When prompted, enter the required information. Refer to the table below for information about each parameter.
palette loginParameter Description Spectro Cloud Console Enter the Palette endpoint URL. When using the Palette SaaS service, enter https://console.spectrocloud.com. When using a self-hosted instance of Palette, enter the URL for that instance.Allow Insecure Connection Bypass x509 server Certificate Authority (CA) verification. Enter yif you are using a self-hosted Palette or Palette VerteX instance with self-signed TLS certificates and need to provide a file path to the instance CA. Otherwise, entern.Spectro Cloud API Key Enter your Palette API Key. Refer to the Create API Key guide for more information. Spectro Cloud Organization Select your Palette organization name. Spectro Cloud Project Select the project you want to register your MAAS account in. Acknowledge Accept the login banner message. Login banner messages are only displayed if the tenant admin enabled a login banner. infoThe
CloudAccount.apiKeyandMgmt.apiKeyvalues in the pcg.yaml file are encrypted and cannot be manually updated. To change these values, use thepalette pcg install --update-passwordscommand. Refer to the PCG command reference page for more information. -
Once you have authenticated your Palette CLI installation, start the PCG installer by issuing the following command. Refer to the table below for information about each parameter.
palette pcg installParameter Description Management Plane Type Select Palette or VerteX. Enable Ubuntu Pro (required for production) Enter yif you want to use Ubuntu Pro and provide an Ubuntu Pro token. Otherwise, entern.Select an image registry type For a non-airgap installation, choose Defaultto pull images from public image registries. This requires an internet connection. For airgapped installations, selectCustomand point to your airgap support VM or a custom internal registry that contains the required images.Share PCG Cloud Account across platform Projects Enter yif you want the cloud account associated with the PCG to be available from all projects within your organization. Enternif you want the cloud account to only be available at the tenant admin scope.Cloud Type Select MAAS. Private Cloud Gateway Name Enter a custom name for the PCG. -
If you want to configure your PCG to use a proxy network, complete the following fields, as appropriate.
infoBy default, proxy environment variables (
HTTPS_PROXY,HTTP_PROXY, andNO_PROXY) configured during PCG installation are propagated to all PCG cluster nodes, as well as the nodes of all tenant workload clusters deployed with the PCG. However, proxy CA certificates are only propagated to PCG cluster nodes; they are not propagated the nodes of tenant workload clusters.Parameter Description HTTPS Proxy Leave this blank unless you are using an HTTPS Proxy. This setting will be propagated to all PCG nodes in the cluster, as well as all tenant clusters using the PCG. Example: https://USERNAME:PASSWORD@PROXYIP:PROXYPORT.HTTP Proxy Leave this blank unless you are using an HTTP Proxy. This setting will be propagated to all PCG nodes in the cluster, as well as all tenant clusters using the PCG. Example: http://USERNAME:PASSWORD@PROXYIP:PROXYPORT.No Proxy Provide a list of local network CIDR addresses, hostnames, and domain names that should be excluded from being a proxy. This setting will be propagated to all the nodes to bypass the proxy server, as well as all tenant clusters using the PCG. Example for a self-hosted environment: my.company.com,10.10.0.0/16.Proxy CA Certificate Filepath (Optional) Provide the file path of a CA certificate on the installer host. If provided, this CA certificate will be copied to each PCG node when deploying the PCG cluster, and the provided path will be used on the PCG cluster nodes. Example: /usr/local/share/ca-certificates/ca.crt.
Note that proxy CA certificates are not automatically propagated to tenant clusters using the PCG; these certificates must be added at either the tenant level or cluster profile level in the OS layer.Configure Proxy CA Certificate for Workload Clusters
If you are configuring proxy CA certificates for your PCG, they must also be added to workload clusters at the tenant level or cluster profile level in the OS layer.
-
If configured at the tenant level, all workload clusters provisioned from the tenant, with the exception of managed Kubernetes clusters (EKS, AKS, and GKE) and Edge clusters, will have the CA certificate injected into their cluster nodes.
-
If configured at the cluster profile level, only workload clusters deployed using the cluster profile will be injected with the CA certificate.
To configure your proxy CA certificate for your workload clusters, use one of the following methods.
- Tenant Settings
- Cluster Profile OS Layer
Take the following approach to propagate your proxy server CA certificate to all workload cluster nodes provisioned from the tenant, with the exception of managed Kubernetes clusters (EKS, AKS, and GKE) and Edge clusters.
-
Log in to Palette as a tenant admin.
-
From the left main menu, select Tenant Settings.
-
From the Tenant Settings Menu, below Platform, select Certificates.
-
Select Add A New Certificate.
-
In the Add Certificate dialog, enter the Certificate Name and Certificate value.
-
Confirm your changes.
Take the following approach to propagate proxy server CA certificates on a per-cluster basis.
-
Log in to Palette.
-
From the left main menu, select Profiles.
-
Choose an existing cluster profile or create a new cluster profile. For more information, refer to the cluster profile guide.
-
In the OS layer of your cluster profile, add your CA certificate to the
contentfield underkubeadmconfig.files.
Example OS layer configurationkubeadmconfig:
preKubeadmCommands:
- echo "Executing pre kube admin config commands"
- update-ca-certificates
- 'systemctl restart containerd; sleep 3'
- 'while [ ! -S /var/run/containerd/containerd.sock ]; do echo "Waiting for containerd..."; sleep 1; done'
postKubeadmCommands:
- echo "Executing post kube admin config commands"
files:
- targetPath: /usr/local/share/ca-certificates/mycom.crt
targetOwner: "root:root"
targetPermissions: "0644"
content: |
-----BEGIN CERTIFICATE-----
***************************
-----END CERTIFICATE------ Select Confirm Updates.
-
-
Enter the following network details.
Parameter Description Pod CIDR Enter the CIDR pool that will be used to assign IP addresses to pods in the PCG cluster. The pod IP addresses should be unique and not overlap with any machine IPs in the environment. Service IP Range Enter the IP address range that will be used to assign IP addresses to services in the PCG cluster. The service IP addresses should be unique and not overlap with any machine IPs in the environment. -
If you selected
Customfor the image registry type, you are prompted to provide the following information.Parameter Description Registry Name Assign a name to the custom registry. Registry Endpoint Enter the endpoint or IP address for the custom registry. Example: https://palette.example.comorhttps://10.10.1.0.Registry Base Content Path Enter the base content path for the custom registry. Example: spectro-images.Configure Registry Mirror Customize the default mirror registry settings. Your system default text editor, such as Vi, will open and allow you to make any desired changes. When finished, save and exit the file. Allow Insecure Connection (Bypass x509 Verification) Bypass x509 CA verification. Enter nif using a custom registry with self-signed SSL certificates. Otherwise, entery. If you entery, you receive a follow-up prompt asking you to provide the file path to the CA certificate.Registry CA certificate Filepath (Optional) Enter the CA certificate for the custom registry. Provide the file path of the CA certificate on the installer host. Example: /usr/local/share/ca-certificates/ca.crt.Registry Username Enter the username for the custom registry. Password Enter the password for the custom registry.
-
Provide the MAAS API key and the MAAS server URL.
Parameter Description MAAS API Key Enter the MAAS API key. MAAS Server URL Enter the MAAS server URL. Example: http://10.1.1.1:5240/MAAS. -
Configure the PCG cluster. The values provided determine which machines should be selected in MAAS for the PCG deployment.
Parameter Description Domain Enter the MAAS domain. Patch OS on boot Indicate whether to patch the OS of the PCG hosts on the first boot. Reboot nodes once OS patch is applied Indicate whether to reboot PCG nodes after OS patches are applied. This applies only if Patch OS on boot is enabled. Availability Zone Enter the availability zones for the PCG cluster. Number of Nodes Enter the number of nodes for the PCG cluster. Available options are 1 or 3. We recommend three nodes for a High Availability (HA) cluster in a production environment. Node Affinity Select yto allow all Palette pods to be scheduled on control plane nodes.warningEnsure the MAAS server has one or more machines in the Ready state for the chosen availability zone and resource pool combination.
-
A new PCG configuration file is generated, and its location is displayed on the console.
Example output==== PCG config saved ====
Location: :/home/demo/.palette/pcg/pcg-20230706150945/pcg.yamlThe Palette CLI begins provisioning a PCG cluster in your MAAS environment. Take the following steps to monitor the progress of the PCG deployment.
-
Log in to Palette as a tenant admin.
-
From the left main menu, select Tenant Settings.
-
From the Tenant Settings Menu, below Infrastructure, select Private Cloud Gateways.
-
Select the PCG cluster being deployed. Use the Events tab to monitor the deployment progress of your PCG cluster.
If you encounter issues during the installation, refer to our PCG Troubleshooting guide. For additional assistance, reach out to our Customer Support team.
warningYou cannot modify a deployed PCG cluster. If you need to make changes to your PCG cluster, you must delete the existing PCG cluster and redeploy it with your updated configurations. For this reason, we recommend you save your PCG configuration file for future use. Use the Palette CLI
--config-onlyflag to save the PCG configuration file without deploying the PCG cluster. Refer to our Generate a Configuration File guide. -
-
To avoid potential vulnerabilities, once your PCG cluster is deployed, remove the
kindimages that were installed in the environment where you initiated the installation.Issue the following command to list all instances of
kindthat exist in the environment.docker imagesExample outputREPOSITORY TAG IMAGE ID CREATED SIZE
kindest/node v1.26.13 131ad18222cc 5 months ago 910MBThen, use the following command template to remove all instances of
kind. Replace<tag>with yourkindimage tag.docker image rm kindest/node:<tag>Consider the following example for reference.
Example commanddocker image rm kindest/node:v1.26.13Example outputUntagged: kindest/node:v1.26.13
Untagged: kindest/node@sha256:15ae92d507b7d4aec6e8920d358fc63d3b980493db191d7327541fbaaed1f789
Deleted: sha256:131ad18222ccb05561b73e86bb09ac3cd6475bb6c36a7f14501067cba2eec785
Deleted: sha256:85a1a4dfc468cfeca99e359b74231e47aedb007a206d0e2cae2f8290e7290cfd
Validate
Once installed, the PCG registers itself with Palette. To verify the PCG is registered, take the following steps.
-
Log in to Palette as a tenant admin.
-
From the left main menu, select Tenant Settings.
-
From the Tenant Settings Menu, below Infrastructure, select Private Cloud Gateways.
-
Verify your PCG cluster is displayed and that it has a green check mark for its Health.
-
Next, from the Tenant Settings Menu, below Infrastructure, select Cloud Accounts.
-
Verify a new MAAS cloud account is displayed.
Next Steps
After you have successfully deployed the PCG in your MAAS environment, you can deploy Kubernetes clusters in your MAAS environment through Palette. Check out the Create and Manage MAAS Clusters guide to learn how to deploy a Kubernetes cluster in MAAS that is managed by Palette.